webmatrix–helpers–antiforgery
On Oct 6 2010, ScottGu (I prefer to call him His Guness : ) ) announced BETA 2 release of WebMatrix. You can check the official release blog post here. You can read the beta 2 release readme here.
I have been following WebMatrix lately. This is one of the blog post series on the WebMatrix helpers. As part of Beta 2 following helpers were added to WebMatrix:
-
Antiforgery -
Bing -
Json -
Themes
In my last blog post i talked about
Bing
helper. This blog post i will be looking in to
“Antiforgery” helper. So lets dive into topic
then.
What is Anti Forgery in web application?
To answer this we should first know what is CSRF –
Cross-Site Request Forgery. Here is the WikiPedia
explanation for this:
Cross-site request forgery, also known as a one-click attack or session riding and abbreviated as CSRF ("sea-surf"[1]) or XSRF, is a type of malicious exploit of a website whereby unauthorized commands are transmitted from a user that the website trusts.[2] Unlike cross-site scripting (XSS), which exploits the trust a user has for a particular site, CSRF exploits the trust that a site has in a user's browser.
To know more about the subject please visit WikiPedia.
Anti Forgery is nothing but one of the mechanism to stop the CSRF attack.
How does the Anti Forgery Helper help us?
This helper works in two folds. First this will help you to embed a anti forgery token as a field in your form. Second this will help you to validate the token whenever you have a form posted. This also has the capability to generate a default token or take a salt to generate a very specific token for you. Using salt is always better so that its like your own secret key for the token generation.
Anti Forgery Helper API in WebMatrix:
We can find the Anti Forgery Helper API in the following assembly:
System.Web.Helpers, Version=1.0.0.0, Culture=neutral, PublicKeyToken=31bf3856ad364e35
This API exposes 2 public methods. Lets have a look at them one by one.
i. public static HtmlString GetHtml(string salt)
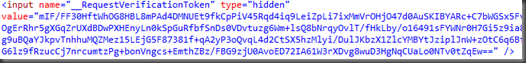
- This method will out put the anti forgery token as a hidden form field in your form. Have a look at the screen shot below:
As you can see this will output the value of the hidden field as a binary encoded data.
- The only parameter to this method – what we call as salt – is optional and default value is “null”. If you provide a salt while generating the anti forgery token using the this method, while validating you need to make sure that you provide the same salt. More on this in the below section.
ii. public static void Validate(string salt)
- This method is used to validate the anti forgery token on the server during your processing.
- This will method will validate your form posting for the presence of the token. If not found meaning if this was a cross site request – will raise a HttpAntiForgeryException.
As you can see the API itself is very neat and cute one : ). It has only 2 methods but does all the work required for your to protect your site from the CSRF. Now lets see some code syntax on how to use this.
Anti Forgery Helper API Usage Syntax:
As you can see from the above code, the usage of the anti forgery helper API syntax is quite simple. You use the GetHtml() method inside the form so that it embeds the token. Then on the server side when you are processing the form – call the Validate() method to check if the request is a cross site request. That’s it. And you have evaded the cross site request attack.
So what exactly happens is – The GetHtml() does 2 things. It creates a HttpCookie for the site which contains the same token value as the form field. In the Validate method you just check if the cookie and the form value tokens match. So if somebody somehow does do a cross site request forgery they will be missing the cookie or the form field for the anti forgery token and that’s how your code will be alerted when you are doing the form processing.
Well this was just my attempt to understand the Helper. Hope it helped you too. Let me know your comments if you do read this. That will help me a lot.
Till next time, Happy coding. Code with passion.